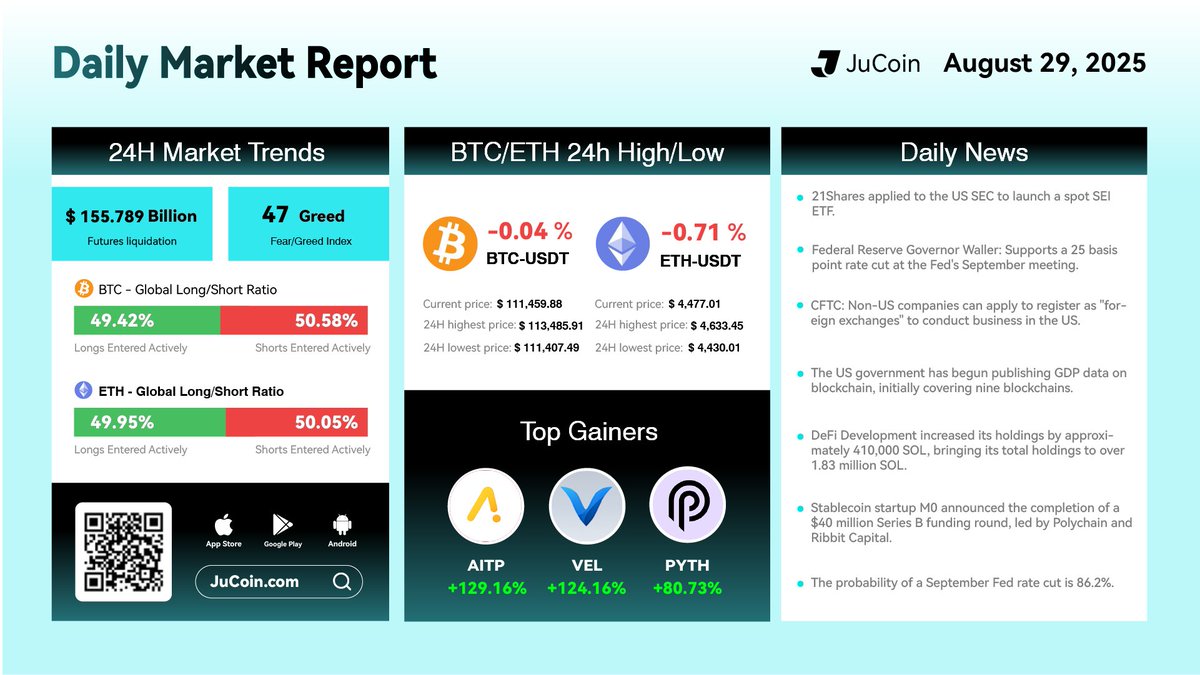
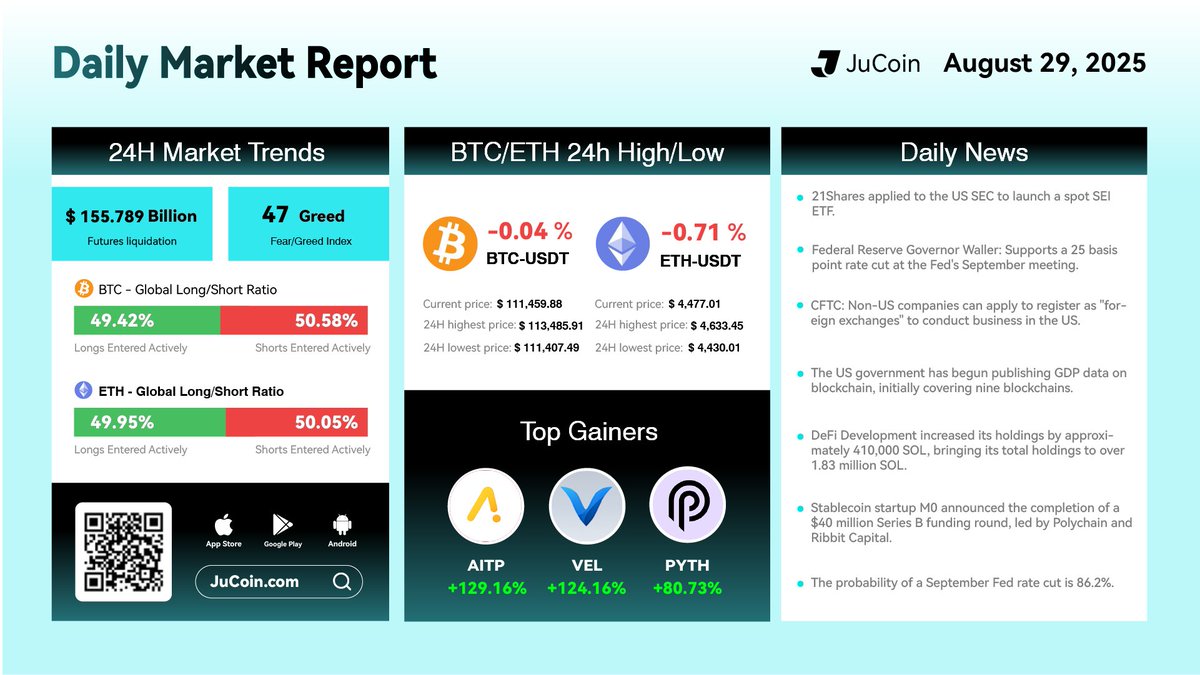
Market Daily Report
Today’s Top Gainers:
$AITP/USDT: 129%
$VEL/USDT: 124%$PYTH/USDT : 80%
$JU Token is close to reach $22 a new ATH
#cryptocurrency #blockchain #finance


Mrconfamm
2025-08-29 07:37
Market Daily Report
免责声明:含第三方内容,非财务建议。
详见《条款和条件》
How Do I Set Up and Use a Hardware Wallet?
Setting up and using a hardware wallet is an essential step for anyone serious about securing their cryptocurrency assets. While the process may seem complex at first, understanding each step ensures that your digital investments are protected against hacking, theft, and other security threats. This guide provides a clear, step-by-step approach to help you confidently set up your hardware wallet and start managing your cryptocurrencies securely.
Choosing the Right Hardware Wallet
Before diving into setup procedures, selecting the appropriate hardware wallet is crucial. Popular options include Ledger Nano series, Trezor Model T, and KeepKey. Consider factors such as compatibility with different cryptocurrencies, security features like PIN protection or biometric authentication, user interface ease of use (touchscreen vs. buttons), and integration capabilities with wallets or exchanges.
Research recent reviews and updates to ensure you select a device that aligns with your security needs and usage preferences. Remember that reputable brands adhere to strict security standards—an important aspect when handling valuable digital assets.
Unboxing Your Hardware Wallet Safely
When you receive your hardware wallet, inspect the packaging carefully for tampering signs. Reputable manufacturers ship devices in sealed packages designed to prevent unauthorized access during transit. Avoid purchasing from unofficial sources; always buy directly from authorized sellers or official websites.
Once unboxed, verify that all components are intact: the device itself, USB cable (if applicable), seed phrase card or booklet, and any accessories provided by the manufacturer.
Initial Setup: Connecting Your Device
The first step in setting up involves connecting your hardware wallet to a computer or compatible mobile device via USB or Bluetooth (depending on model). Ensure you're using secure connections—preferably direct USB links rather than shared networks—to minimize potential interception risks during setup.
Follow on-screen instructions provided by the device’s interface—these typically involve powering on the device by pressing specific buttons or following prompts displayed on its screen if it has one.
Creating a New Wallet & Securing Your Seed Phrase
During initial setup:
Choose a PIN Code: You will be prompted to create a PIN code—a critical layer of physical security preventing unauthorized access if someone else gets hold of your device.
Generate Seed Phrase: The device will generate a 12-24 word seed phrase (also called recovery phrase). This phrase is vital because it acts as a master key allowing you to restore access if the hardware is lost or damaged.
Write Down Your Seed Phrase: Carefully record this seed phrase on paper using pen—never store it digitally where hackers could access it—and store it securely offline in multiple safe locations away from thefts or natural disasters.
Confirm Seed Phrase: To ensure accuracy during setup, you'll likely be asked to re-enter some words from your seed phrase as confirmation steps within the interface.
This process establishes an offline backup method for restoring funds without relying solely on proprietary software services—a core principle of cold storage solutions enhancing overall asset safety.
Installing Companion Software & Firmware Updates
Most hardware wallets require companion applications installed onto computers (e.g., Ledger Live for Ledger devices) or mobile apps compatible with their firmware versions:
- Download these applications only from official sources.
- Follow installation instructions carefully.
- Check for firmware updates immediately after setup; manufacturers often release patches addressing vulnerabilities or adding new features.
Keeping firmware updated ensures maximum protection against emerging threats while maintaining compatibility with new cryptocurrencies and smart contract functionalities where supported.
Adding Cryptocurrencies & Managing Assets
Once configured:
- Connect your hardware wallet via its companion app.
- Add supported cryptocurrencies by selecting them within this software interface.
- Transfer funds securely from exchanges into addresses generated directly through your hardware wallet—this process ensures private keys remain offline at all times during transactions.
Always verify transaction details before confirming transfers; many wallets display transaction info directly on their screens for added assurance against phishing scams targeting user interfaces elsewhere online.
Using Your Hardware Wallet Safely During Transactions
When conducting transactions:
- Connect your device only through trusted computers/devices in secure environments.
- Enter PIN codes directly into the physical device rather than third-party terminals whenever possible.
- Confirm transaction details physically on-device screens instead of relying solely on computer displays which could be compromised via malware attacks.4.. Use two-factor authentication methods offered by some models when available—for example biometric verification—to add extra layers of security during operations involving significant amounts of cryptocurrency holdings.
Best Practices for Maintaining Security
To maximize safety over time:
– Regularly update both firmware and companion apps following manufacturer guidelines– Never share seed phrases under any circumstances– Store backup copies securely offline– Be cautious about phishing attempts impersonating support services– Avoid connecting devices in insecure public Wi-Fi environments unless necessary precautions are taken
Troubleshooting Common Setup Issues
If encountering problems such as failure to recognize connected devices:
- Ensure cables are functioning correctly
- Restart both computer/device and hardware wallet
- Verify drivers are installed properly if applicable
- Consult official support resources provided by manufacturers
Final Tips Before Fully Relying On Your Hardware Wallet
While setting up provides robust protection measures initially,
remember that ongoing vigilance remains essential:
- Always keep backups updated separately from primary seeds
- Stay informed about latest cybersecurity threats targeting crypto users
- Consider multi-signature setups if managing large portfolios
By following these comprehensive steps—from choosing an appropriate model through secure management—you can confidently utilize your hardware wallet as part of an effective strategy for safeguarding digital assets in today’s evolving crypto landscape.
Note: For optimal E-A-T principles adherence — expertise comes from understanding technical processes; authority stems from following best practices recommended by reputable brands; trust builds through careful handling of sensitive information like seed phrases—and transparency about potential risks involved at every stage enhances overall credibility among users seeking reliable crypto storage solutions
What Are the Inherent Risks of Interacting with DeFi Protocols?
Decentralized Finance (DeFi) has emerged as a transformative force in the financial industry, offering innovative ways to lend, borrow, trade, and earn yields without traditional intermediaries. While DeFi provides increased accessibility and transparency, it also introduces a range of inherent risks that users must understand before engaging. This article explores these risks comprehensively to help users navigate the complex landscape of DeFi safely.
Understanding Smart Contract Vulnerabilities
At the core of DeFi protocols are smart contracts—self-executing code that automates financial transactions based on predefined rules. Although they enable trustless operations, smart contracts are susceptible to bugs and vulnerabilities. Historically significant incidents like the DAO hack in 2016 demonstrated how exploited vulnerabilities could lead to massive losses; approximately 3.6 million Ether were drained due to a reentrancy bug[1]. These vulnerabilities often stem from coding errors or overlooked edge cases during development. As smart contracts are immutable once deployed, fixing such issues post-launch can be challenging and costly.
To mitigate this risk, rigorous security audits by third-party firms are essential before deploying new protocols or updates. Additionally, ongoing monitoring and bug bounty programs incentivize community participation in identifying potential flaws early.
Liquidity Risks in Decentralized Pools
Liquidity is vital for smooth trading and borrowing activities within DeFi ecosystems. Many protocols rely on liquidity pools—collections of tokens supplied by users—to facilitate transactions without centralized order books[2]. However, these pools can face liquidity shortages during periods of high volatility or market downturns. Insufficient liquidity can lead to slippage—where trades execute at unfavorable prices—or even transaction failures.
For example, during sudden market crashes or large trades (known as "whale" movements), prices may swing sharply due to low liquidity levels[3]. Users participating in yield farming or providing liquidity should be aware that their assets might become illiquid if market conditions deteriorate unexpectedly.
Market Volatility Impact
Cryptocurrencies used within DeFi platforms are inherently volatile assets; their values can fluctuate dramatically over short periods[3]. Such volatility directly affects collateral valuations in lending protocols and impacts yield calculations for farmers earning interest or rewards. A sudden price drop could trigger liquidation events where collateral is sold off automatically at unfavorable rates—a process known as "liquidation risk."
This unpredictability underscores the importance for users engaging with leverage-based strategies or staking assets: they must closely monitor market trends and set appropriate risk parameters like collateralization ratios to avoid unexpected losses.
Regulatory Uncertainty Surrounding DeFi
The regulatory landscape for DeFi remains largely undefined globally[4]. Governments and regulators are increasingly scrutinizing decentralized platforms due to concerns about consumer protection, money laundering risks, tax evasion potential—and whether existing laws apply effectively within decentralized environments.
This ambiguity exposes users and platform operators to legal uncertainties; regulations could change abruptly leading to restrictions on certain activities or shutdowns of platforms altogether[4]. Staying informed about evolving legal frameworks is crucial for participants who wish to avoid unintended compliance violations while maintaining access.
Security Threats: Phishing & Hacks
Beyond technical vulnerabilities within smart contracts themselves lies an array of security threats targeting individual users’ funds[5]. Phishing attacks remain prevalent—attackers impersonate legitimate services via fake websites or emails designed specifically to steal private keys or seed phrases necessary for wallet access(5). Once compromised, hackers can drain user accounts instantly.
High-profile hacks such as Wormhole’s $320 million breach in 2022 highlight how security lapses at bridge infrastructure points pose significant risks [10], emphasizing that no component is immune from attack vectors targeting cross-chain interoperability solutions used widely across DeFi ecosystems.
Users should adopt best practices including multi-factor authentication (MFA), hardware wallets when possible—and always verify URLs—to reduce susceptibility toward phishing schemes [5].
Reentrancy Attacks: A Persistent Threat
Reentrancy attacks exploit specific vulnerabilities where malicious actors repeatedly call functions within a contract before previous executions complete[6]. This loophole allows attackers unauthorized access—potentially draining funds from affected protocols if not properly guarded against reentrant calls(6).
The infamous DAO hack was an early example illustrating this threat’s severity [1], prompting developers worldwide toward implementing safeguards like mutexes (mutual exclusions) into their codebases today [6].
Ensuring robust coding standards combined with formal verification methods significantly reduces reentrancy-related exploits' likelihood across new protocol deployments.
Front-Running & Sandwich Attacks Exploiting Transaction Ordering
In blockchain networks where transaction ordering isn’t strictly controlled by centralized authorities—the phenomenon known as front-running becomes problematic.[7] Traders with faster access may observe pending transactions via mempool data—and place their own orders ahead intentionally (“front-run”) —altering prices unfavorably for others(7).
Sandwich attacks take this further by placing one order just before a target trade while another immediately afterward—effectively “sandwiching” it—to manipulate asset prices temporarily.[7] These tactics undermine fair trading principles within DEXs like Uniswap but also pose financial risks for regular traders unfamiliar with such exploits.[7]
Mitigation strategies include implementing time-weighted average pricing mechanisms (TWAP)and utilizing privacy-preserving techniques such as zero-knowledge proofs where feasible .
Dependence on Oracles & Data Integrity Issues
Many advanced DeFi applications depend heavily on external data sources called “oracles” — which provide real-time information like asset prices,[8] interest rates,[8] etc., necessary for executing automated decisions accurately(8). However , inaccuracies stemming from faulty data feeds—or malicious manipulation—can cause severe miscalculations leading either into unwarranted liquidationsor incorrect payouts(8).
Protocols employing multiple independent oracle sources coupled with decentralization techniques aimto improve resilience against false data injection but cannot eliminate all associated risks entirely .
Navigating the Risks: Best Practices & Future Outlook
While inherent dangers exist across various facets—from technical bugs through regulatory shifts—the key lies in adopting comprehensive risk management strategies . Regularly auditing codebases , diversifying investments , employing secure wallets , staying updated about legal developments ,and understanding protocol mechanics form partof prudent engagement practices .
Recent developments indicate increased focus on enhancing security measures—including more rigorous audits post-hack incidents—as well as efforts towards clearer regulation frameworks aimed at protecting investors while fostering innovation . As the ecosystem matures—with improved standards around transparency,safety,and compliance—the overall safety profile will likely improve over time—but vigilance remains essentialfor all participants involvedin decentralized finance activities.
How Are Transaction Fees Determined in the Crypto Space and How Do They Work?
Understanding transaction fees in the cryptocurrency ecosystem is essential for both new users and seasoned investors. These fees are not just a cost of using blockchain networks; they play a vital role in maintaining network security, prioritizing transactions, and managing congestion. This article provides a comprehensive overview of how transaction fees are determined, how they function across different blockchain platforms, and recent developments influencing their dynamics.
What Are Cryptocurrency Transaction Fees?
Cryptocurrency transaction fees are charges paid by users to process their transactions on a blockchain network. Unlike traditional banking systems where third-party institutions handle processing costs, crypto networks rely on miners or validators who confirm transactions. These fees incentivize participants to include transactions in blocks and ensure the network remains secure and operational.
Transaction fees serve multiple purposes:
- Compensating miners/validators for their work
- Preventing spam attacks that could clog the network
- Prioritizing urgent transactions over less critical ones
Without appropriate fee structures, networks could become congested or vulnerable to malicious activities.
Factors Influencing Transaction Fee Calculation
The amount users pay as a fee depends on several key factors:
1. Network Congestion
When many users attempt to send transactions simultaneously—such as during market surges—network congestion occurs. This leads to longer confirmation times unless higher fees are paid to prioritize processing.
2. Transaction Complexity
More complex transactions require more computational resources:
- Larger data size (more bytes)
- Multiple inputs/outputs
- Use of advanced scripting techniques (e.g., multi-signature wallets)
These factors increase the required fee because they demand more processing power from validators.
3. Blockchain Protocols
Different blockchains have unique mechanisms for calculating and applying transaction fees:
- Bitcoin: Uses a fee per byte model; higher data size means higher fee.
- Ethereum: Employs "gas," which measures computational effort needed; gas price fluctuates based on demand.
Each protocol's design influences how users estimate costs before submitting transactions.
How Do Different Blockchains Determine Fees?
Understanding specific blockchain models helps clarify how transaction costs work:
Bitcoin’s Fee Model
Bitcoin operates on a first-in, first-out basis where miners select unconfirmed transactions with the highest attached fee per byte (sat/vB). Users can set their own fee rates; paying more increases chances of faster confirmation during high traffic periods.
Ethereum’s Gas System
Ethereum uses "gas" units representing computational steps required for executing smart contracts or simple transfers. Users specify a gas limit (maximum units willing to spend) and gas price (amount willing to pay per unit). The total fee equals gas used × gas price. During busy times, gas prices tend to spike due to increased demand for block space.
Other Networks’ Approaches
Some newer blockchains adopt dynamic pricing algorithms or tiered models designed for scalability while maintaining decentralization principles—examples include Binance Smart Chain or Solana with lower average fees but different prioritization mechanisms.
The Role of User Behavior in Fee Dynamics
User behavior significantly impacts overall network activity:
- During bullish markets or major events like token launches, increased trading volume raises congestion.
- DeFi applications often require multiple sequential transactions—for example, borrowing collateral or swapping tokens—which cumulatively increase total transaction volume.
This surge can cause temporary spikes in average transaction fees as users compete for limited block space.
Recent Developments Affecting Transaction Fees
Recent news highlights some notable trends impacting crypto transaction costs:
Regulatory Changes & Market Events
Legislation such as New Hampshire's Bitcoin reserve cap may influence trading activity levels by restricting certain investments—potentially reducing congestion temporarily but also affecting overall market liquidity which indirectly impacts fee levels over time.
High-profile Incidents & Market Volatility
Events like investigations into meme coins linked with political figures reveal vulnerabilities related to insider trading profits through trading strategies that involve high-frequency trades—these activities often lead to increased network load due to rapid trade execution demands resulting in higher transactional costs across platforms like Ethereum or Bitcoin when markets react sharply.
Similarly, large corporate holdings such as MicroStrategy's significant Bitcoin losses reflect broader market volatility that can ripple into increased transactional activity driven by traders adjusting positions rapidly—a phenomenon known as “volatility-driven congestion.”
Impact of Regulation & Market Trends on Future Fees
As governments scrutinize cryptocurrencies further through regulations aimed at preventing illicit activities while promoting transparency:
- We may see stricter rules around minimum acceptable fees,
- Implementation of layer-two solutions like Lightning Network (Bitcoin) or rollups (Ethereum) designed specifically for reducing mainnet load,which could stabilize long-term costs but might introduce new complexities regarding user experience and security considerations.
Additionally, growing adoption within decentralized finance ecosystems continues pushing up overall throughput requirements—and consequently increasing average transaction costs unless scaling solutions mature sufficiently.
Practical Tips For Managing Cryptocurrency Transaction Costs
To optimize your experience when sending crypto assets:
- Monitor current network conditions via tools like mempool explorers before initiating large transfers.
- Adjust your offered fee based on urgency: choose lower rates during off-hours when traffic is lighter.
- Consider using layer-two solutions if available—they often provide faster confirmations at reduced costs compared with mainnet operations.
- Stay informed about protocol upgrades aimed at improving scalability without compromising decentralization standards.
By understanding how various factors influence cryptocurrency transaction fees—from protocol designs through user behaviors—you can better navigate this evolving landscape. As markets grow more active amid regulatory shifts and technological innovations, staying aware will help you manage costs effectively while contributing positively toward maintaining healthy decentralized networks capable of supporting future growth.
Keywords: cryptocurrency transaction fees | blockchain confirmation times | gas system Ethereum | Bitcoin mining rewards | network congestion | Layer 2 scaling solutions | DeFi impact onFees
How Cryptocurrency Transactions Are Confirmed and Finalized on a Network
Understanding how cryptocurrency transactions are confirmed and finalized is essential for anyone interested in blockchain technology, digital currencies, or investing in crypto assets. This process ensures the security, integrity, and transparency of transactions across decentralized networks. In this article, we will explore the key components involved in transaction confirmation and finalization, recent technological advancements, potential challenges, and their broader implications.
The Role of Blockchain Technology in Transaction Confirmation
At the core of cryptocurrency transaction processing lies blockchain technology—a decentralized ledger that records all transactions across a network of computers called nodes. Each transaction is grouped into blocks that are cryptographically linked to form an immutable chain. Once a block is added to the blockchain, altering any information within it becomes virtually impossible due to cryptographic protections.
This structure provides transparency because every participant can verify transactions independently by accessing the shared ledger. It also enhances security by eliminating single points of failure; unlike traditional centralized systems, no single entity controls the entire database.
How Transactions Are Verified on a Cryptocurrency Network
When you initiate a cryptocurrency transfer—say sending Bitcoin or Ethereum—the transaction must be verified before it becomes part of the official record. Verification involves multiple steps:
- Transaction Validation: Nodes on the network check whether your wallet has sufficient funds and if your transaction adheres to protocol rules.
- Broadcasting: Validated transactions are broadcasted across nodes for inclusion into upcoming blocks.
- Grouping into Blocks: Miners or validators collect pending transactions into blocks for processing.
The verification process ensures that only legitimate transactions are recorded on the blockchain, preventing issues like double-spending or fraudulent activity.
Mining and Its Impact on Transaction Confirmation
Mining plays a pivotal role in confirming cryptocurrency transactions—particularly those using Proof of Work (PoW) mechanisms like Bitcoin. Miners compete to solve complex mathematical puzzles; solving these problems validates new blocks containing recent transactions. The first miner to find a valid solution broadcasts their block for network acceptance.
This process requires significant computational power and energy consumption but provides robust security because altering confirmed data would require redoing proof-of-work calculations across many miners—a practically impossible feat at scale.
Once mined successfully, a block is added to the chain with cryptographic links securing its place within history. This addition signifies that included transactions have been confirmed by consensus among miners or validators depending on the mechanism used.
Confirmations: When Is a Transaction Considered Final?
After inclusion in an initial block—known as having one confirmation—the number increases as subsequent blocks are added atop it (confirmations). Most cryptocurrencies consider 1–6 confirmations sufficient before considering funds fully secure for large transfers or sensitive operations.
For example:
- Bitcoin typically requires 3–6 confirmations.
- Ethereum often considers 12 confirmations adequate due to faster block times but may vary based on context.
Multiple confirmations reduce risks associated with potential forks or malicious attacks such as double-spending attempts since reversing several subsequent blocks becomes computationally infeasible over time.
Understanding Blockchain Forks: Temporary Disruptions
Occasionally during network operation, different nodes might temporarily have divergent versions of the blockchain—a situation known as forks. These can occur due to software updates (planned forks), disagreements over validation rules (unplanned forks), or malicious attacks like 51% control scenarios where an entity gains majority hashing power.
Most forks resolve quickly through consensus mechanisms—either reverting temporary splits via chain reorganizations or adopting new protocols during hard forks—ensuring eventual consistency across all participants while maintaining trustworthiness.
Recent Advances Improving Transaction Processing
The landscape of cryptocurrency confirmation processes continues evolving rapidly:
Scalability Solutions: Technologies such as sharding divide networks into smaller parts for parallel processing; layer 2 solutions like Lightning Network enable off-chain microtransactions reducing congestion.
Speed Enhancements: Protocol upgrades aim at reducing confirmation times—for instance, Ethereum's transition toward proof-of-stake aims at faster finality compared with traditional PoW systems.
Security Improvements: Adoption of quantum-resistant algorithms seeks protection against future threats posed by quantum computing capabilities which could compromise current cryptography standards.
Challenges Facing Cryptocurrency Confirmation Processes
Despite technological progress, several hurdles remain:
Regulatory Uncertainty
Different jurisdictions impose varying rules regarding crypto activities which influence how exchanges handle transaction reporting and compliance measures affecting user experience and trustworthiness levels within ecosystems.
Security Risks
Phishing scams targeting private keys; wallet hacks leading to loss; vulnerabilities exploited through network attacks—all threaten user confidence despite inherent protocol security features designed around decentralization principles.
Scalability Constraints
High fees during peak periods discourage small-value transfers while slow confirmation times hinder real-time applications such as point-of-sale payments—prompting ongoing efforts toward more scalable solutions.
Environmental Concerns
Energy-intensive mining operations raise sustainability questions about cryptocurrencies relying heavily on PoW algorithms; this has accelerated interest toward eco-friendly alternatives like Proof-of-Stake (PoS).
Broader Implications: Financial Inclusion & Innovation
Efficiently confirming digital asset transfers opens doors beyond simple peer-to-peer payments—it fosters financial inclusion by providing unbanked populations access via mobile devices without traditional banking infrastructure barriers. Additionally,
cryptocurrencies fuel investment opportunities attracting retail investors seeking diversification alongside institutional players entering markets previously considered niche.
Blockchain’s technological innovations extend beyond finance into supply chains ensuring provenance tracking; healthcare improving data integrity; voting systems enhancing transparency—all benefiting from reliable transaction finality mechanisms rooted in decentralized consensus models.
By understanding how cryptocurrencies confirm and finalize transactions through complex yet transparent processes involving mining protocols, consensus mechanisms—and ongoing innovations—you gain insight into building trust within these digital ecosystems while appreciating their challenges ahead.
Keywords: Cryptocurrency confirmation process | Blockchain validation | Transaction finality | Mining & proof-of-work | Consensus mechanisms | Blockchain scalability | Digital currency security
What Is Liquidity Mining in the DeFi Ecosystem?
Liquidity mining is a fundamental concept within the decentralized finance (DeFi) landscape that has significantly contributed to its rapid growth. It involves incentivizing users to supply liquidity—essentially, funds—to decentralized exchanges (DEXs) and other financial protocols. This process not only enhances the trading experience by reducing slippage but also fosters community participation and decentralization.
Understanding Liquidity Mining: How Does It Work?
At its core, liquidity mining encourages users to deposit their cryptocurrencies into liquidity pools on DeFi platforms. These pools are used to facilitate trading, lending, or other financial activities without relying on centralized intermediaries. In return for providing this liquidity, participants earn rewards—often in the form of governance tokens or interest payments.
For example, when a user deposits ETH and USDT into a DEX like Uniswap or SushiSwap, they become a liquidity provider (LP). As trades occur within these pools, LPs earn transaction fees proportional to their share of the pool. Additionally, many protocols distribute native governance tokens as incentives—these tokens can grant voting rights and influence protocol development.
This mechanism aligns with DeFi's ethos of decentralization by allowing individual users rather than centralized entities to control significant parts of financial operations. It also helps improve market efficiency by increasing available liquidity for various assets.
The Evolution of Liquidity Mining in DeFi
Liquidity mining emerged as an innovative solution to traditional finance’s limitations regarding capital requirements and central control over markets. Unlike conventional market-making—which often requires substantial capital reserves—liquidity mining democratizes access by enabling anyone with crypto assets to participate actively.
In recent years, yield farming—a subset of liquidity mining—has gained popularity among crypto enthusiasts seeking higher returns. Yield farms allow users to deposit assets into specific pools managed across multiple protocols like Compound or Yearn.finance; these platforms then optimize yields through complex strategies involving staking and lending.
The rise of yield farming has led some investors to deploy large sums into DeFi projects rapidly but has also introduced new risks such as impermanent loss—the potential loss incurred when token prices fluctuate relative to each other—and smart contract vulnerabilities.
Key Benefits for Participants
Participating in liquidity mining offers several advantages:
- Earning Rewards: Users receive governance tokens that can be held or traded; these often appreciate over time if the platform succeeds.
- Interest Income: Some protocols provide interest payments similar to traditional savings accounts.
- Influence Over Protocol Development: Governance tokens enable holders voting rights on key decisions affecting platform upgrades or fee structures.
- Supporting Decentralization: By contributing funds directly into protocols, LPs help maintain open-access markets free from central authority control.
However, it’s essential for participants always considering risks such as token volatility and smart contract security issues before engaging extensively in liquidity mining activities.
Challenges Facing Liquidity Mining
While lucrative opportunities exist within DeFi’s ecosystem through liquidity mining practices, several challenges threaten sustainability:
Market Volatility
Governance tokens earned via liquidity provision tend to be highly volatile due to fluctuating cryptocurrency prices and market sentiment shifts. This volatility can diminish long-term profitability if token values decline sharply after initial rewards are earned.
Regulatory Risks
As authorities worldwide scrutinize DeFi activities more closely—including yield farming—they may impose regulations that restrict certain operations or classify some tokens as securities. Such regulatory uncertainty could impact user participation levels significantly.
Security Concerns
Smart contract exploits have been notable setbacks for many platforms; high-profile hacks like those targeting Ronin Network highlight vulnerabilities inherent in complex codebases lacking thorough audits. These incidents erode trust among participants and can lead to substantial financial losses if exploited maliciously.
Scalability Issues
As demand increases during periods of high activity within popular protocols like Aave or Curve Finance—the network congestion causes elevated transaction fees (gas costs) and slower processing times which hinder seamless user experiences especially during peak periods.
The Future Outlook: Opportunities & Risks
The ongoing transition from Ethereum 1.x towards Ethereum 2.0 aims at improving scalability through proof-of-stake consensus mechanisms which could make transactions faster while reducing costs—a positive development for liquid providers seeking efficiency gains amid growing demand.
Furthermore,
- Competition among different protocols continues driving innovation,
- New incentive models emerge regularly,
- Cross-chain integrations expand access across multiple blockchains,
all promising further growth avenues for liquid miners.
However,
regulatory developments remain unpredictable,security remains paramount with ongoing efforts toward better auditing practices,and scalability challenges must be addressed comprehensively before mass adoption becomes truly sustainable.
Final Thoughts on Liquidity Mining's Role in DeFi
Liquidity mining remains one of the most impactful innovations shaping decentralized finance today—it enables broader participation while fueling platform growth through incentivized asset provision. Its success hinges on balancing attractive rewards against inherent risks such as price volatility, security vulnerabilities, regulatory uncertainties—and ensuring robust infrastructure capable of handling increased activity efficiently.
As DeFi continues evolving rapidly—with technological advancements like layer-two solutions promising enhanced scalability—the landscape around liquidity provisioning will likely become more sophisticated yet safer for everyday investors seeking exposure beyond traditional banking systems.
By understanding how it works—and recognizing both its opportunities and pitfalls—participants can better navigate this dynamic environment while contributing meaningfully toward building resilient decentralized financial ecosystems rooted firmly in transparency and community-driven governance.
Keywords: Liquidity Mining , Decentralized Finance , Yield Farming , Crypto Rewards , Smart Contract Security , Blockchain Protocols , Governance Tokens , Market Volatility
